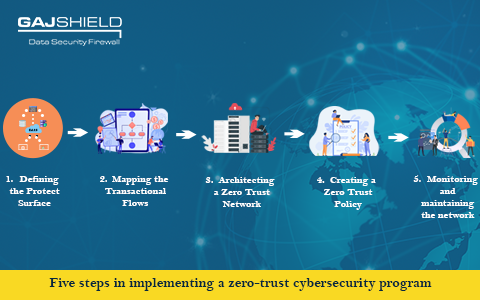
Five steps in implementing a zero-trust cybersecurity program
Zero Trust is a cyber security model which considers any request, whether it is within or outside an organisation, as a potential breach. It requires every request to be verified, encrypted and authorised before granting access. The execution of this program combines advanced technologies such as identity protection, risk-based multi-factor authentication, and robust cloud technology to verify or authenticate a system or user and then considers access as per the request.In traditional or on-premises network architecture, devices and users connecting to the networks were regarded as “trusted.” The activity could be limited using a firewall and hardwired connections. However, this trust model was depleted with the emergence of wireless networks. Zero trust is a way for companies to reduce risk by continuously verifying access.
Basic Principles of a Zero Trust Program
These are the basic principles that guide a Zero Trust program:
- Assume every request as a potential breach
- Assume an organization-owned network or server is not more trustworthy or different than an open network
- Constantly analyse and evaluate risks
- Continually enact risk mitigation measures
- Minimise asset and user access to resources
- Always authenticate and authorise security and identity for every access request received
The Scope of Implementation in a Zero Trust Program
Every company looking to implement a zero-trust program is not doing so under the same or similar circumstances. Although it is one of the best methods to secure cyber assets, various needs should be taken into consideration by different organisations. There are two types of trust models:
- Pure Zero Trust Creation - It is also known as the Greenfield approach. Mainly new businesses take up this model as they have no cybersecurity architecture, or those looking for a complete reconstruction of their existing systems and are starting from scratch.
- Hybrid and Perimeter System - This variety of zero trust is more widely used. Companies seek to incorporate the program of zero trust into their cyber defences of an already existing perimeter-focused cybersecurity system.
Even though the second method is more commonly used, the same principles apply to the greenfield or pure zero trust creation, but the scope and scale for each step differ significantly.
Steps for implementing Zero-Trust Program
Implementing this program is a steady and constantly introspective process. Therefore, it will help for businesses to know the steps to create the ideal zero-trust program:
1. Defining the Protect Surface
The surface of attack is constantly expanding, making it difficult to shrink, define or protect against, and working tirelessly to reduce it is not viable in today’s ever-evolving landscape of threat. Therefore with zero trust, an organisation can determine and focus on its protect surface rather than its attack surface on a macro level.
The protect surface comprises sensitive data, assets, applications and services, also known as DAAS, which are the most valuable resources for the organisation. Examples of DAAS in protecting surface may include -
- Data - personally identifiable information, intellectual property, banking card information, and protected health information
- Assets - IoT devices (internet of things), SCADA (supervisory control and data acquisition) controls, physical equipment, etc.
- Application - Custom software
- Services - Dynamic Host Configuration Protocol (DHCL), Active Directory, etc.
Once the organisation defines its protection surface, it can create a micro perimeter with its policy statements which are precise, understandable, and limited.
2. Mapping the Transactional Flows
The way the traffic travels across a network decides how it should be safeguarded. Hence, it is crucial to understand the contextual insights around the interdependencies of a company’s DAAS. Analysing how particular resources function allows the organisation to enforce proper controls will provide valuable context. These controls will help protect their data and not cause any hindrance to the workings of a business.
3. Architecting a Zero Trust Network
The networks of Zero Trust are fully customisable and are not obtained from a universal or single design. The architecture is, in fact, constructed based on the protected surface. After the organisation has defined its protection surface and mapped the flows respective to the requirements of its business, it can create a Zero Trust architecture. They can start the process via a Next-Generation firewall. It acts as a segmentation gateway through which the company can enforce additional layers of access and inspection control to layer 7 (the topmost layer of the open systems interconnect model, also known as the application layer).
4. Creating a Zero Trust Policy
After the network is built, the company will need to formulate a Zero Trust policy. This can be done by using the Kipling method - a process of listing down questions either randomly or with a more specific purpose and answering based on the situation at hand. This will allow the organisation to determine who will have access to the resources. Using this method will define the following questions:
- Who can access a resource?
- What is the application being utilised to access a resource inside the protected surface?
- When is the resource on the protected surface being accessed?
- Where is the location of the packet (data which is sent over a network and divided into smaller segments)?
- How is a user able to access this packet through a particular application?
With such stringent policy enforcement, an organisation can be assured that only legitimate and allowed traffic is permitted to access the secured data.
5. Monitoring and maintaining the network
The final step constitutes reviewing all logs, whether external or internal, all the way through layer 7 and focusing on operational aspects of the Zero Trust program. Since the model of zero trust is a reiterative process which inspects and logs all traffic, it will provide beneficial insights as to how to enhance the network over time.
Zero Trust is not a technology project but a shift in organisational culture. Companies should address and assess the potential impact zero trust programs can have on end-users, business stakeholders, operational teams and relevant third parties. This protection can help build a strong foundation of trust. Elimination of implied trust from an enterprise will most likely be the key to developing trustworthy transformation digitally.
Gajshield’s data security solutions can help you build an ideal zero-trust security ecosystem to protect your data. Kindly contact us to know more about our data security solutions.
Get In Touch With Us
Subscribe to our Newsletter
2026 © GajShield Infotech (I) Pvt. Ltd. All rights reserved.
